Hacking
What is hacking? Where does this practice come from? What is its relationship to art in general, and to media art in particular? Let us give the concept a rough, historical profile.
1. Hacking is a form of writing, more specifically, a form of re-writing. It presupposes the existence of a text and a ‘code’, the system from which a text draws its meaning and its authority. English borrowed this German word in the middle ages. Its physical connotation – to cut something with rough blows – had by the 18th century already gained a literary dimension, a negative sense describing artless or journalistic writing. This doesn’t mean hacking is fundamentally literary, but it does mean that the pre-history of hacking may be found in literary practices, including those of the oral traditions.
2. Hacking also has a genealogy in artistic practice. The Situationist strategy of détournement, for example – of hijacking words and images, turning their weapons on themselves – inspired much of the ‘culture-jamming’ of the early web era. In the 1970s and 80s, media and activist art was already mining the rich shafts of Dada and Surrealist misappropriation. But hacking has much deeper roots, in pre-modern cultures where the creative reiteration of well-known narrative codes was not the avant-garde exception, but the everyday rule. Western thought has only recently begun to update its caricature of ‘traditional’ cultures, bound by the superstitious repetition of ancient, ‘classical’ models. The folk cultures surrounding and nourishing these traditions were often characterized by ribald, irreverent détournement. (Hence the value of a theory of the carnivalesque, for historicizing today’s DIY and ‘alternative’ media cultures.[1])
3. Hacking is not necessarily a political practice, but politics can’t get very far without hacking. Propaganda was perhaps the first modern, organized form of hacking, when it crossed from a tactical into a strategic modus operandi. Dictators don’t have new ideas. They remix old ones, splicing together new myths – new code – out of malleable ideas of the past. (The paradigm of modernity’s most successful PR-hack, Fascism, was not an image of an industrial tomorrow, but of a folksy yesteryear.) Propaganda is susceptible to hacking and hacking lends itself to propaganda, for they are made of the same stuff. Whatever our causes, and especially in a post-authoritarian landscape like Southeast Asia’s, before embracing hacking we should reflect on its conflicted inheritance.
4. Hacking is not necessarily good; nor is it necessarily subversive. Its association with ‘hacktivism’ and the open-source programming movement does wonders for its image, but let us not forget that hacking is a practice, not an ethics. It is not the exclusive domain of do-gooder activists, but a parasitic culture largely dependent on power, and just as likely to serve it as to undermine it. The libertarian credentials of shadowy hacker ‘communities’ like Anonymous and LulzSec are the stuff of Robin Hood-style fantasy. Their better-known stunts may be populist and anti-establishment, but the truth is that these networks are fundamentally neither liberal, nor democratic. Their skills may be put to dark purposes, and when sold, their services command a price way beyond the budgets of concerned netizens.
5. Hacking, in recent decades, has become fundamentally informatic. But if hacking is now a key form of contemporary culture, it’s not because this is the age of hacking. It’s because this is the age of the code, because the codes governing social and political life have become increasingly digital ones, and because all other codes are being rendered in this electronic form.[2] This is not just the story of neo-liberal capital and its ‘frictionless’ orbit around the globe. It is also, since the advent of recombinatory biology in the 1970s, the fate of life itself. This is why biotechnology and media art are increasingly hard to separate, and why hacking has a certain bond with environmentalism. Most of the world’s farmers are not yet cyborgs, but they know better than us that code is the medium, and the currency, of life.
David Teh,
Singapore April 2012
[1]Mikhail Bakhtin, Rabelais and his world, trans. Helene Iswolsky (Bloomington: Indiana University Press, 1984).
[2]Jean Baudrillard, Symbolic Exchange and Death [1976], trans. Iain Hamilton Grant (London, Thousand Oaks and New Delhi: SAGE Publications, 1993).
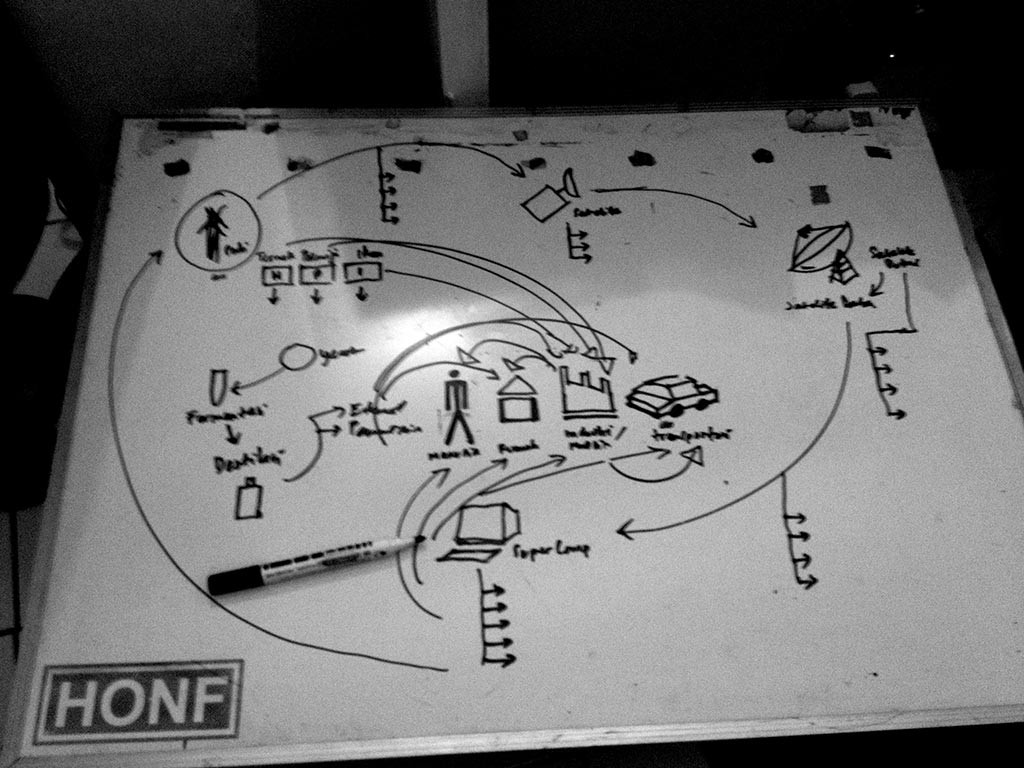
These are the steps after akcnowledge the problem that happened as Project Backround, and Project Research as the basic steps to do the following realization:
Data Mining
Data mining means we collect all the information through online media to build the database for the project, while the social data collecting was done through field research and expert meeting.
Satellite Hacking
Satellite hacking activity is an activity to have data ‘access’ from Indonesia satellite for mainly, weather & climate information, soil structures, winds, rainfall etc or any other data that is related for farming and important for farmers knowledge.
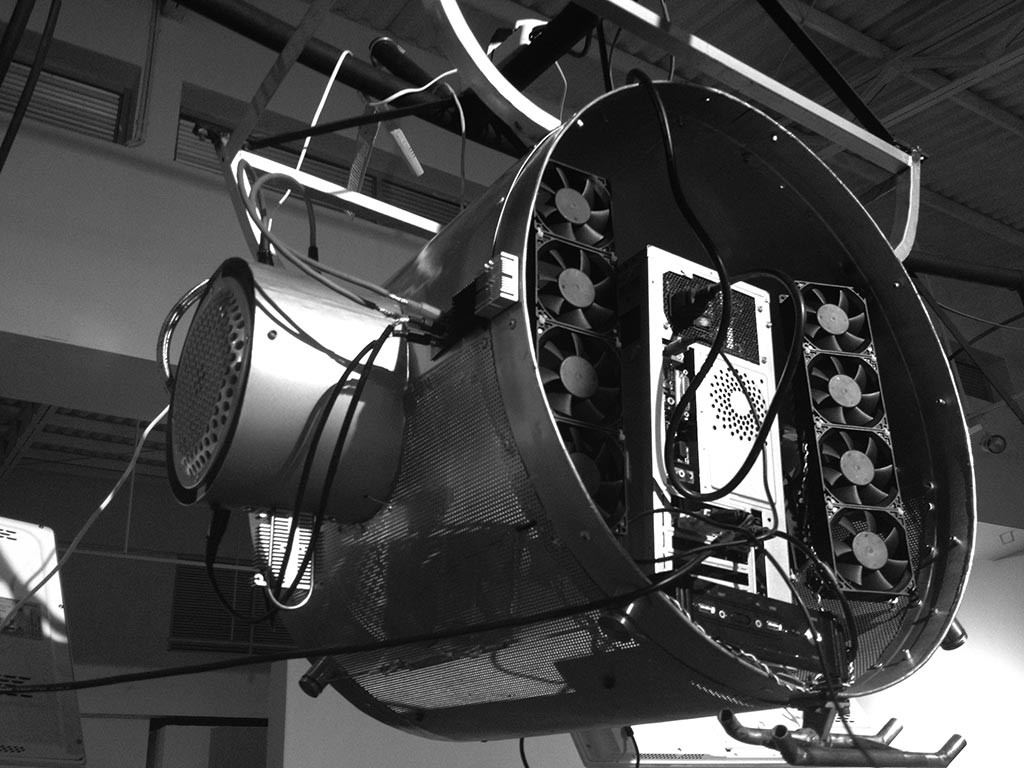
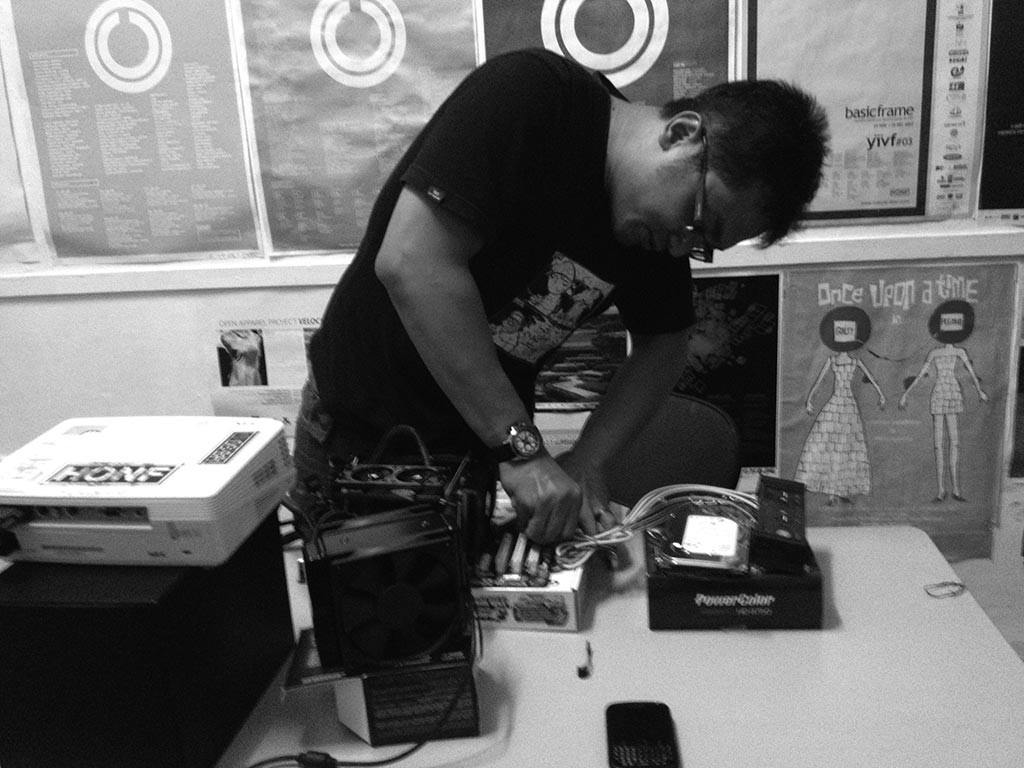
Build Super Computer
The ‘Super Computer’ was bulit to do the data processing that we collect by accessing the satellite. This Super Computer generaly process all the data using GPU process to speed up the result.